Running a business may never be totally smooth sailing, but it doesn’t have to be a complete grind all the time either. Managing complexities with your business’ technology is a good way to ensure that things move ahead with some efficiency. Today, we look at four ways to effectively handle complexities in the realm of business technology.
About Coleman Technologies
Coleman Technologies has been serving the British Columbia area since 1999, providing IT Support such as technical helpdesk support, computer support and consulting to small and medium-sized businesses. Our experience has allowed us to build and develop the infrastructure needed to keep our prices affordable and our clients up and running.
Understanding IT
Get the Knowledge You Need to Make IT Decisions
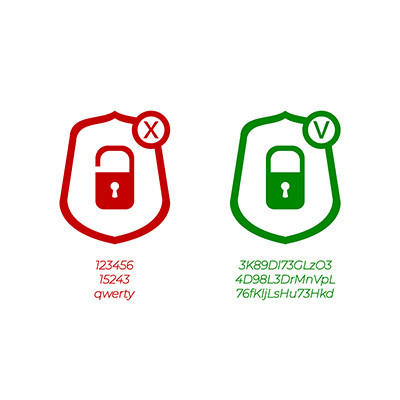
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Contact Us
20178 96 Ave C400
Langley, British Columbia V1M 0B2
Mon to Fri 7:00am–5:00pm
Coleman Technologies Awards & Memberships